Cross-Border Data Transfer
Published: January 2026
An Assurance-Led Model for Lawful, Defensible Data Movement in Africa
Executive Summary
Cross-border data transfer is no longer an exception—it is the default operating condition of modern digital systems. Cloud platforms, cybersecurity services, analytics pipelines, customer-support tooling, and AI workloads routinely move data across national boundaries as part of normal operation.
Across Africa, data-protection laws are advancing rapidly. However, organizations continue to struggle—not because cross-border transfer is always prohibited, but because they cannot
prove
that such transfers are lawful, controlled, and continuously governed.
Policies exist. Contracts exist. Legal opinions exist.
Assurance often does not.
This paper presents an assurance-led approach to cross-border data transfer, centered on the Fidelra Assurance Framework (FAF™). It demonstrates how lawful data movement is achieved, evidenced, governed, and sustained over time—without relying on one-time compliance exercises.
1. The Real Problem with Cross-Border Data Transfer
Organizations treat cross-border data transfer as a legal decision:
- Is there a lawful basis?
- Is there an approved safeguard?
- Is consent required?
These questions are necessary—but insufficient.
In practice, regulators, auditors, boards, and partners ask different questions:
- Where does the data actually flow today?
- Who approved the transfer and owns the risk?
- What safeguards are active right now—not last year?
- How do you know this has not drifted?
- What evidence can you produce immediately?
The gap between legal permission and operational proof is where most compliance failures occur.
Lawful transfer that cannot be proven—on demand and over time—is not defensible.
2. Why “Easier” Approaches Fall Short
Many existing publications focus on:
- Legal frameworks and adequacy concepts
- Regional harmonization and policy alignment
- High-level recommendations
While valuable, these approaches rarely address:
- how controls operate in real systems
- how evidence is generated continuously
- how assurance is maintained after change
The result is compliance intent, not compliance assurance.
3. The Assurance-Led Position
Cross-border data transfer must be governed as a system condition, not a one-time decision.
This means:
- Controls operate continuously
- Evidence is produced by design
- Accountability is explicit
- Deviation is detectable
- Assurance survives audits, incidents, and time
This is the purpose of FAF™.
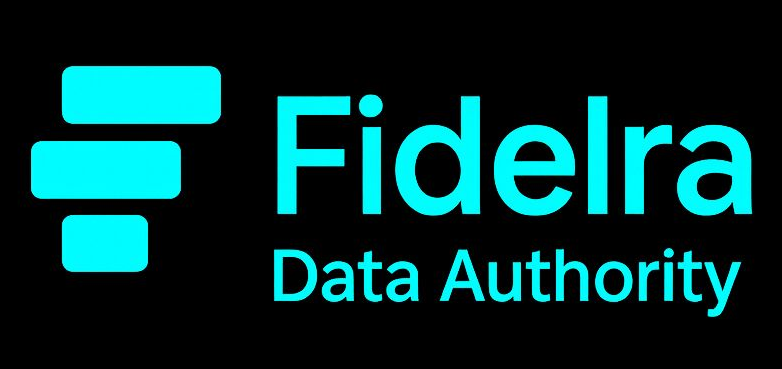
4. The FAF™ Cross-Border Data Transfer Assurance Model
Figure 1: The FAF™ Cross-Border Data Transfer Assurance Model shows how lawful data movement is achieved and sustained through concurrent controls, continuously generated evidence, and executive-level assurance.
FAF™ is not a checklist.
It is assurance architecture.
FAF™ treats cross-border transfer as an assurance system operating across five concurrent domains:
- Compliance
- Governance
- Resilience
- Modernization
- Automation
Each domain answers a question that regulators and executives care about—and no domain operates in isolation.
5. How Is Lawful Cross-Border Data Transfer Achieved?
Answer:
By satisfying
all five FAF™ domains concurrently.
A transfer is defensible only when:
- it is lawfully justified (Compliance)
- explicitly approved and owned (Governance)
- resilient to cross-border incidents (Resilience)
- supported by defensible architecture (Modernization)
- continuously monitored with live evidence (Automation)
Failure in any one domain weakens overall assurance.
Q6. What Is Required to Achieve It?
The impact of assurance maturity becomes clear during audits and investigations:
6.1 Foundational Inputs (Visibility and Ownership)
Before any transfer can be governed, organizations must establish:
- complete cross-border data-flow mapping
- identification of origin and destination jurisdictions
- data classification and sensitivity
- defined purpose of transfer
- a named accountable owner
Without visibility and ownership, assurance cannot exist.
6.2 Control Inputs (What Must Be in Place)
FAF™ requires controls across multiple dimensions:
- Compliance controls
Lawful basis, safeguards, regulatory alignment - Governance controls
Transfer approvals, accountable ownership, vendor and subprocessor oversight - Technical controls
Encryption, access control, region and workload segmentation - Operational controls
Incident response, breach notification, cross-border recovery coordination.
7. How Is Evidence Shown?
FAF™ treats evidence as a system output, not an audit artifact.
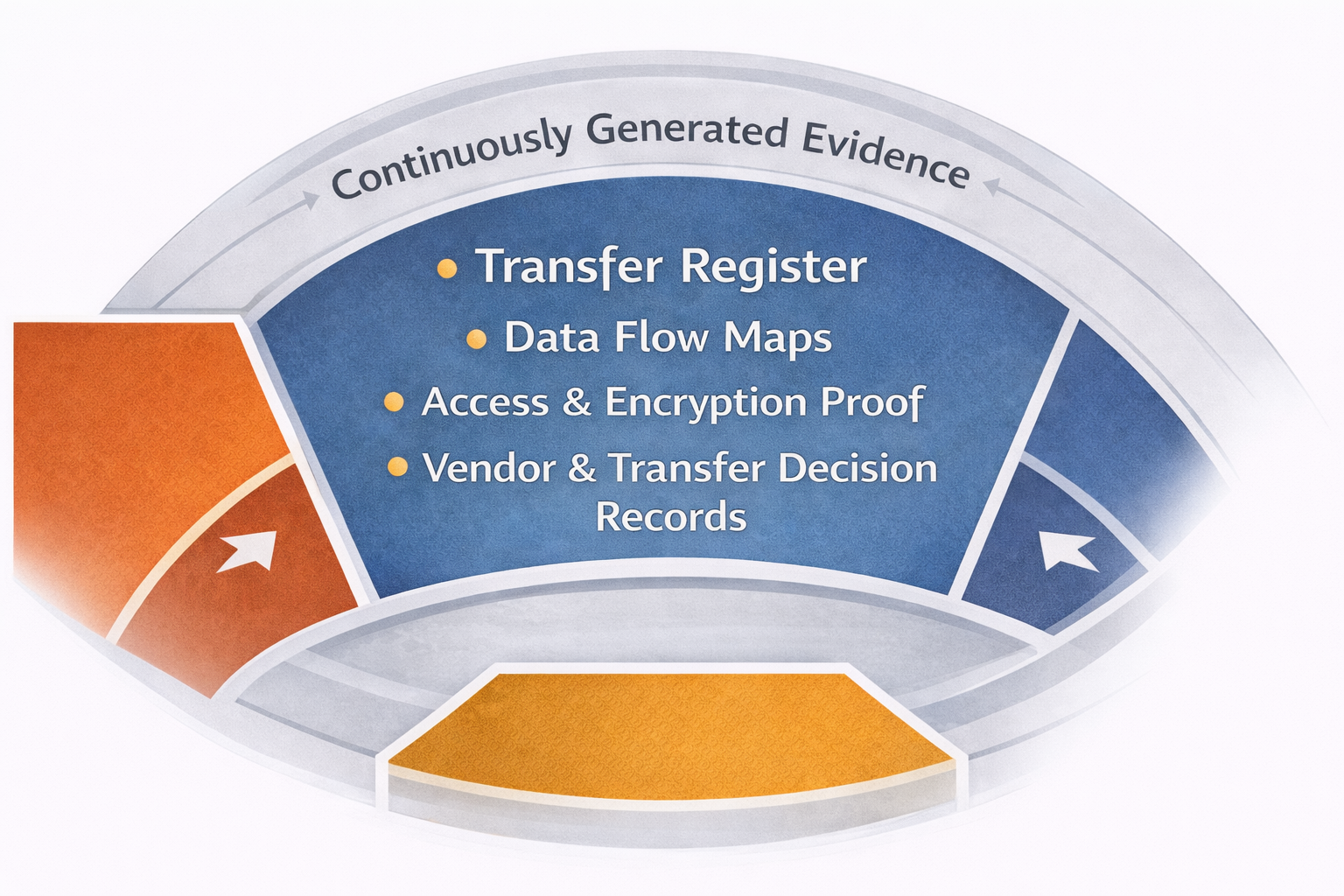
Figure 2: Continuously generated evidence produced by FAF™ ensures cross-border data transfer remains provable, auditable, and defensible over time.
Evidence must be:
- current
- traceable
- attributable
- reproducible on demand
Typical evidence includes:
- cross-border transfer registers
- data-flow maps
- access and encryption proof
- vendor and transfer-decision records
If evidence must be rebuilt under pressure, assurance does not exist.
8. What Is Considered “Acceptable”?
FAF™ defines a minimum defensible transfer posture.
A transfer is acceptable when:
- the data flow is known and documented
- the transfer decision is justified and approved
- safeguards are active and verifiable
- evidence is continuously generated
- deviations are visible and governed
This enables organizations to demonstrate
defensibility, not perfection.
9. How Is Assurance Maintained Over Time?
Assurance degrades unless actively maintained.
Triggers requiring reassessment include:
- new vendors or subprocessors
- cloud region or architecture changes
- expanded access privileges
- new data uses or analytics
- regulatory updates
FAF™ enforces:
- periodic reassessment cycles
- change-triggered reviews
- evidence refresh and drift detection
- exception tracking with time-bound remediation
10. How Are Monitoring, Governance, and Enforcement Applied?
Monitoring
- continuous access and region monitoring
- configuration-drift detection
- alerts on vendor or control changes
Governance
- explicit accountability and escalation paths
- executive and board-level visibility
Enforcement
- transfer suspension when safeguards fail
- vendor re-approval requirements
- controlled, time-bound exceptions
Governance is effective only when deviation is observable and actionable.
11. The Questions Most Organizations Avoid—And FAF™ Answers
FAF™ explicitly answers:
- Who is accountable if a transfer is challenged?
- How quickly can evidence be produced?
- What data must never leave the jurisdiction?
- How can a transfer be paused or unwound?
- How is this scaled across countries and platforms?
- How is compliance sustained without rebuilding it each audit cycle?
Assurance answers these questions before regulators ask them.
12. The Fidelra Position
Cross-border data transfer succeeds when governed as a continuous assurance system.
FAF™:
- establishes minimum defensible posture
- enforces concurrent control domains
- generates audit-ready evidence continuously
- enables lawful, scalable data movement
Africa’s digital future depends not merely on data movement, but on trusted data movement. Organizations that can demonstrate lawful, controlled, and continuously assured cross-border operations will lead in resilience, innovation, and institutional credibility.
FAF™ exists to make that defensibility real.
About Africa Insights
Africa Insights is Fidelra’s institutional research and thought-leadership platform examining data assurance maturity, regulatory evolution, and modernization risk across the African continent.